analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
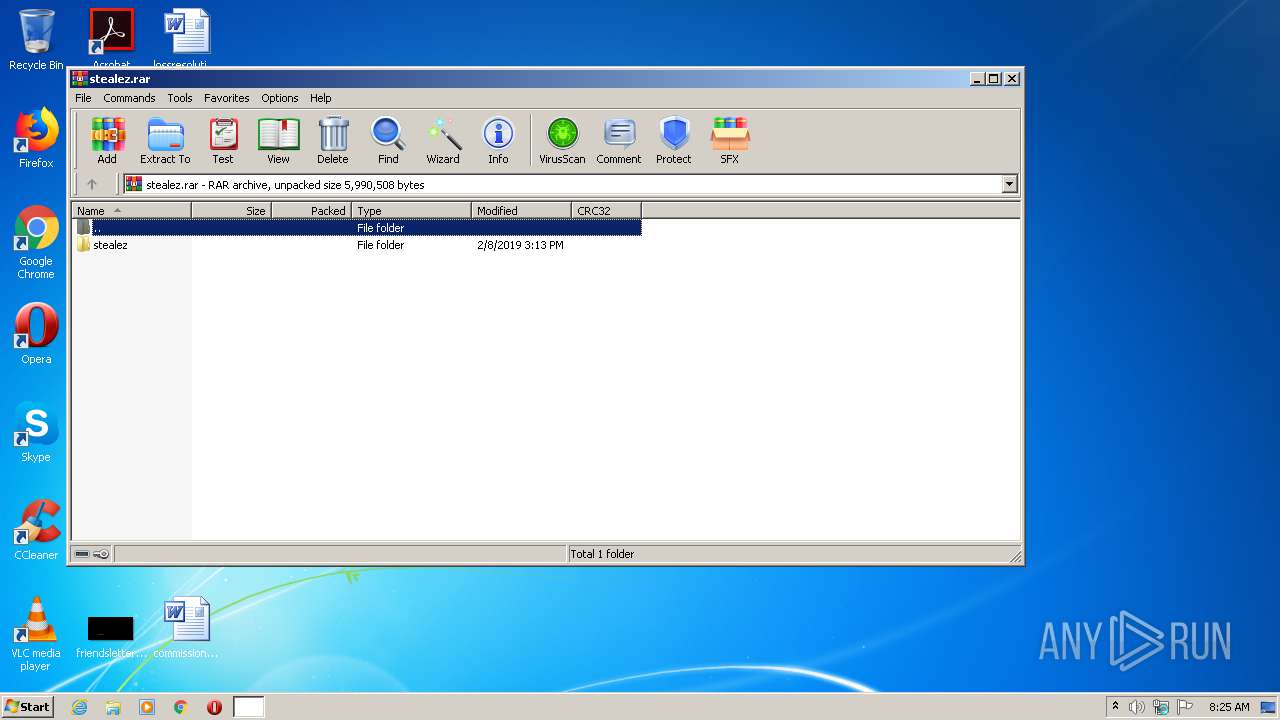
| File name: | stealez.rar |
| Full analysis: | https://app.any.run/tasks/5449210a-8316-4e7f-99c7-2d532453a972 |
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2020, 07:24:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F7B8D867C737694A34AF1DEB6DF69AC4 |
| SHA1: | AF9B9E531E28DF8E0B708D75F469EA8F495BC578 |
| SHA256: | 7F37AB90D76A9A22EA78983ECD93EBF556C4D7AEAB3E57979831C052C89BE292 |
| SSDEEP: | 98304:VsaQF/zGs7CT4xIfIOGckLZVi5+eTD/xK6UcLuCCuUxhb8H8t9+zlf3cjs3mscwg:gSs7u4xWIOZkFVPeTlGcSjuUkm9e9cOm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3996)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3996)
Reads the hosts file
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3996)
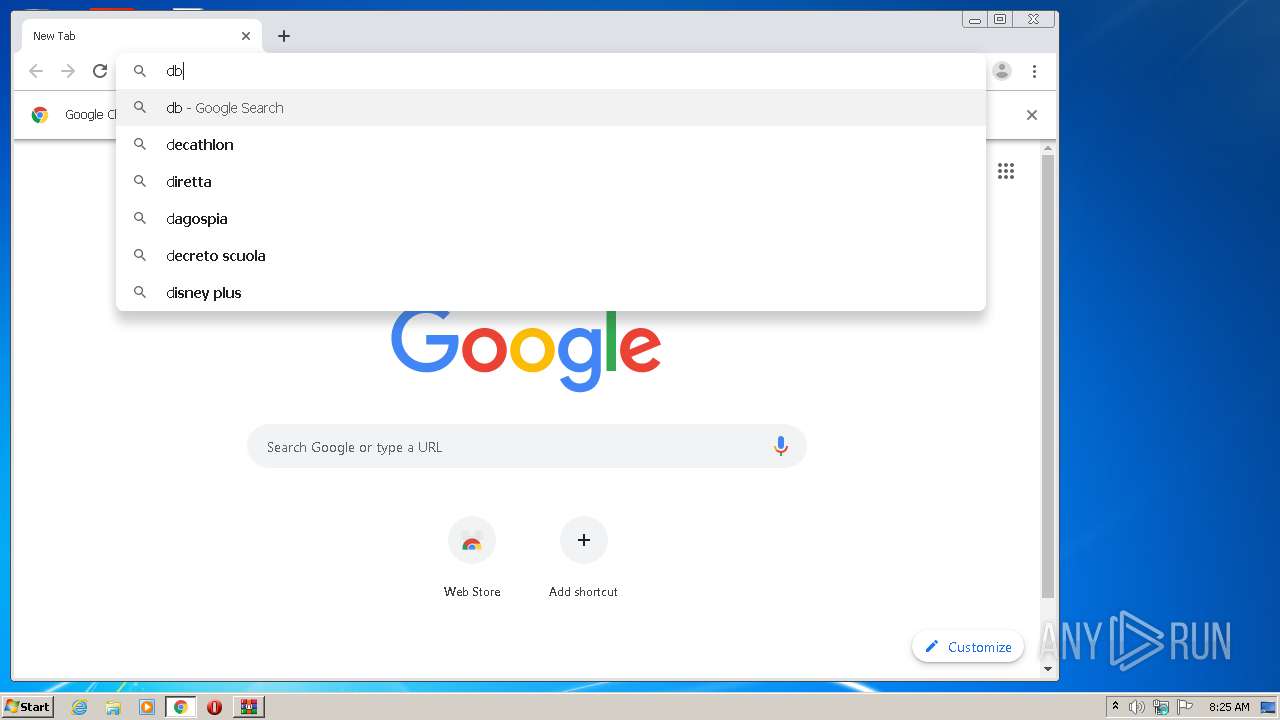
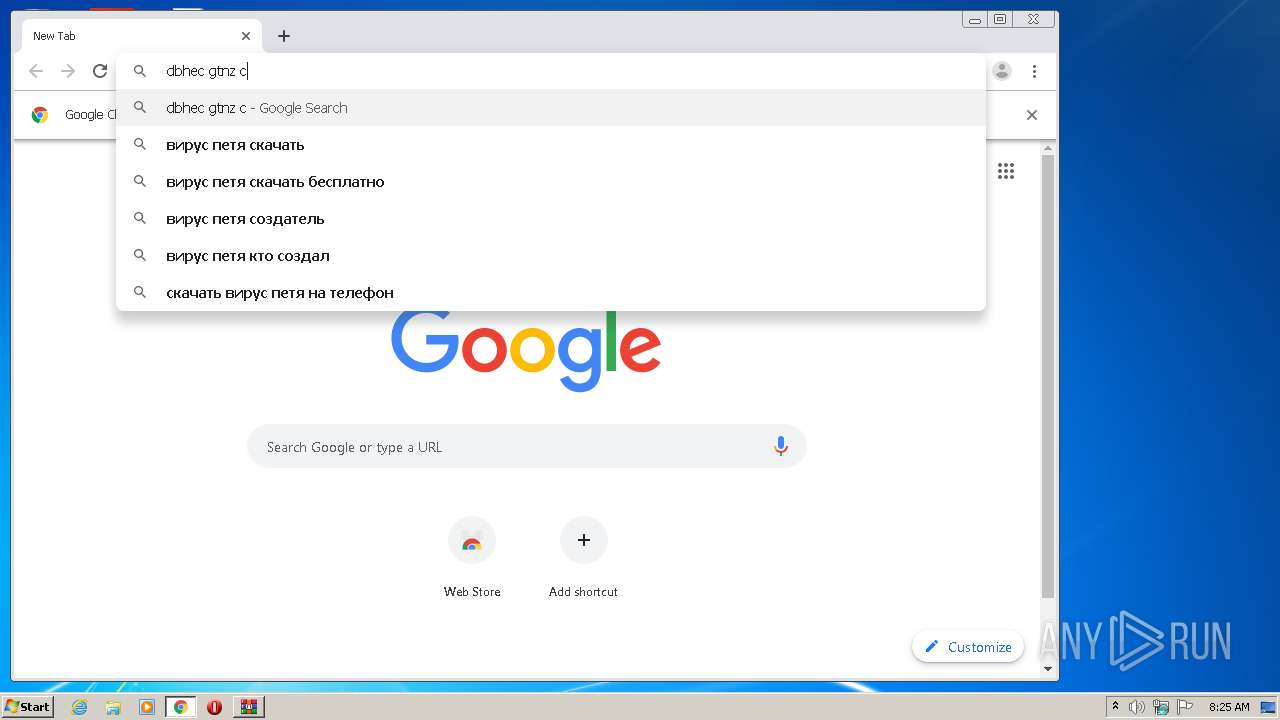
Manual execution by user
- chrome.exe (PID: 3996)
Application launched itself
- chrome.exe (PID: 3996)
Reads settings of System Certificates
- chrome.exe (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
85
Monitored processes
50
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2256 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\stealez.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.60.0 | ||||
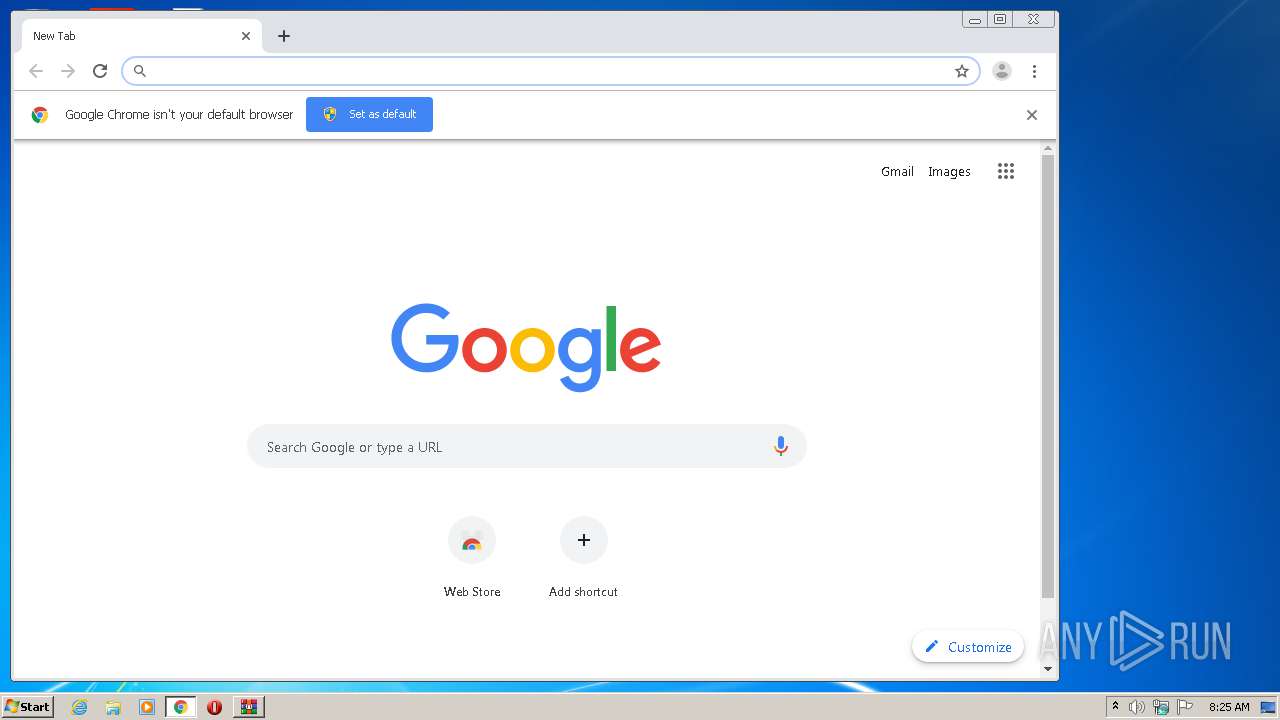
| 3996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f07a9d0,0x6f07a9e0,0x6f07a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4000 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1079874933171627248,203540837015487874,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8819257613432992836 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1079874933171627248,203540837015487874,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7862325076935714777 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1079874933171627248,203540837015487874,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16601484756148381754 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1079874933171627248,203540837015487874,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5426888981314753023 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1079874933171627248,203540837015487874,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1376010692183428067 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1079874933171627248,203540837015487874,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9847333116950596077 --mojo-platform-channel-handle=3300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
1 210
Read events
1 090
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
235
Text files
324
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EDC9655-F9C.pma | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6ed371f8-03d6-4a2d-8696-f3b1d341f5ff.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:A9C81BA506E2A0D898698EAF075EBE5C | SHA256:92FB2125FB5A0B877B76C4E3409B250EFF394804C7F24E236FBE162E1054AF90 | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:702AEC53DCDCFEA33C4BE3D2F888473E | SHA256:D16286D6EE0EB33E7907EE4FCB8FDB6B5A54E5A56BFAF99A9C2451D239BC9765 | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15e817.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
128
TCP/UDP connections
174
DNS requests
107
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2888 | chrome.exe | GET | 302 | 172.217.23.99:80 | http://www.google.ru/coop/cse/brand?form=cse-search-box&lang=ru | US | html | 265 b | whitelisted |
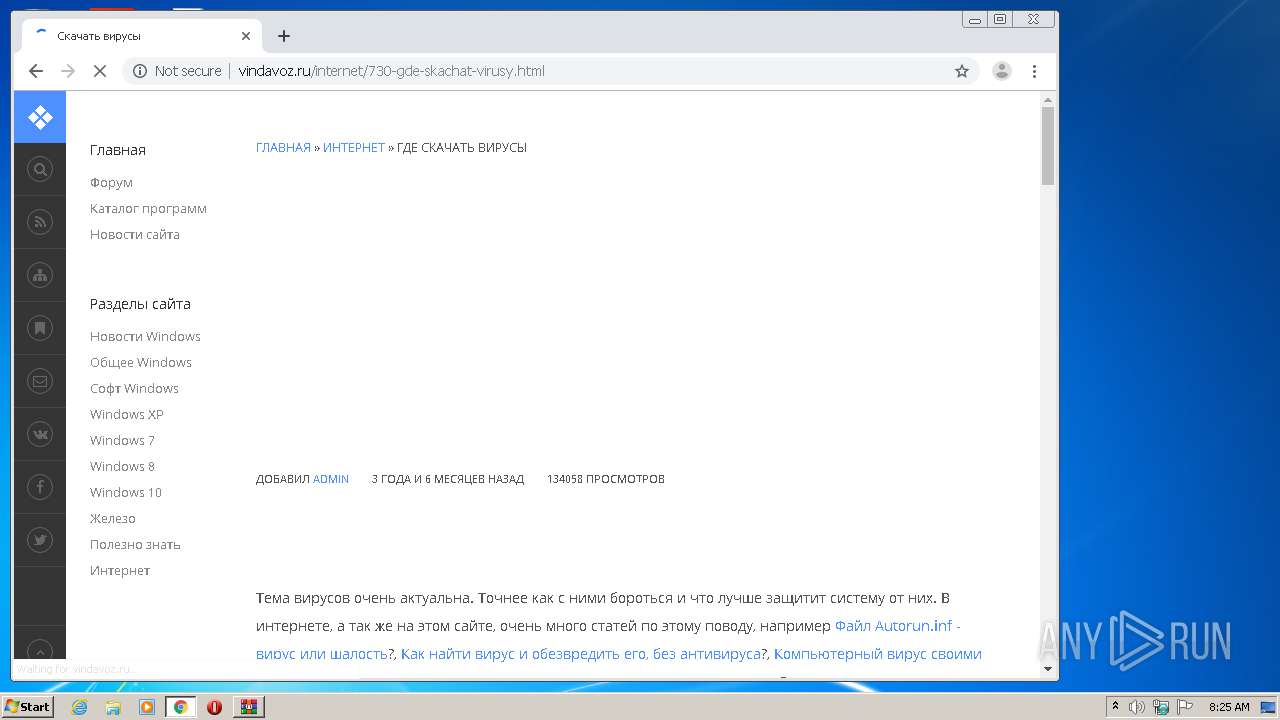
2888 | chrome.exe | GET | 200 | 91.218.228.14:80 | http://vindavoz.ru/engine/classes/min/index.php?charset=windows-1251&f=engine/classes/js/bbcodes.js,engine/classes/highslide/highslide.js&9 | RU | text | 16.3 Kb | whitelisted |
2888 | chrome.exe | GET | 200 | 91.218.228.14:80 | http://vindavoz.ru/templates/vindanew/style/bbcodes.css | RU | text | 1.25 Kb | whitelisted |
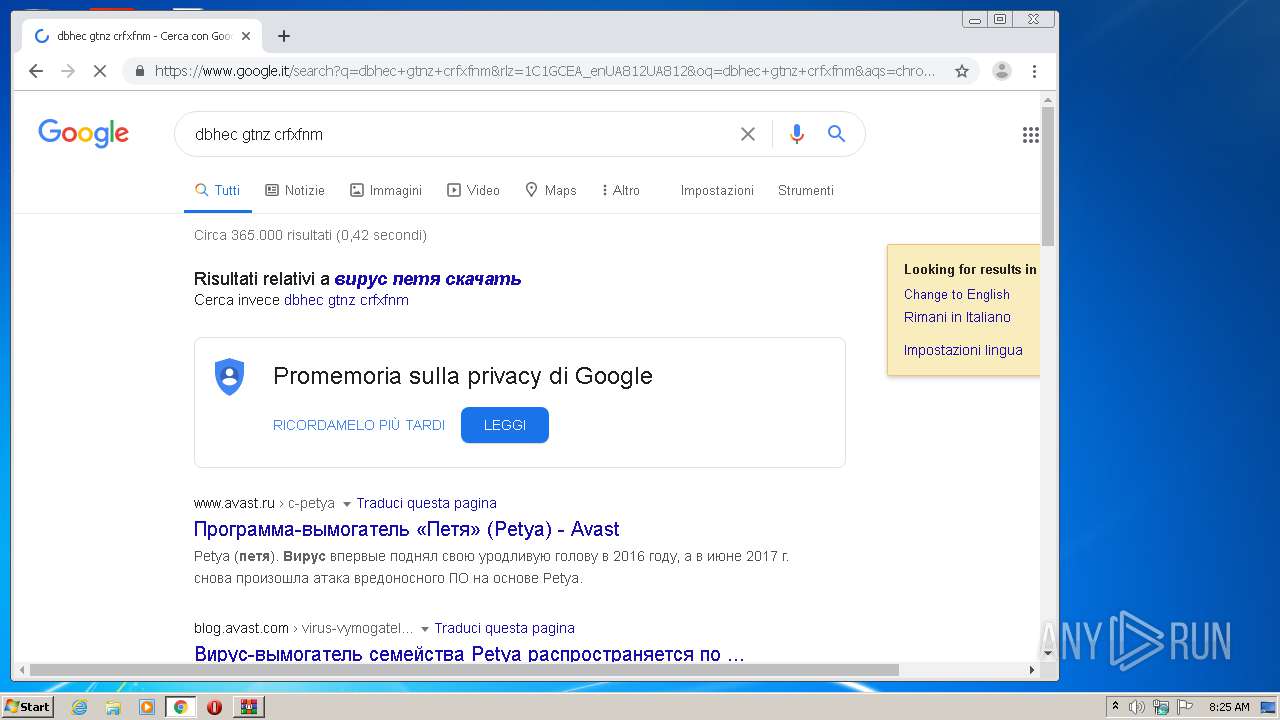
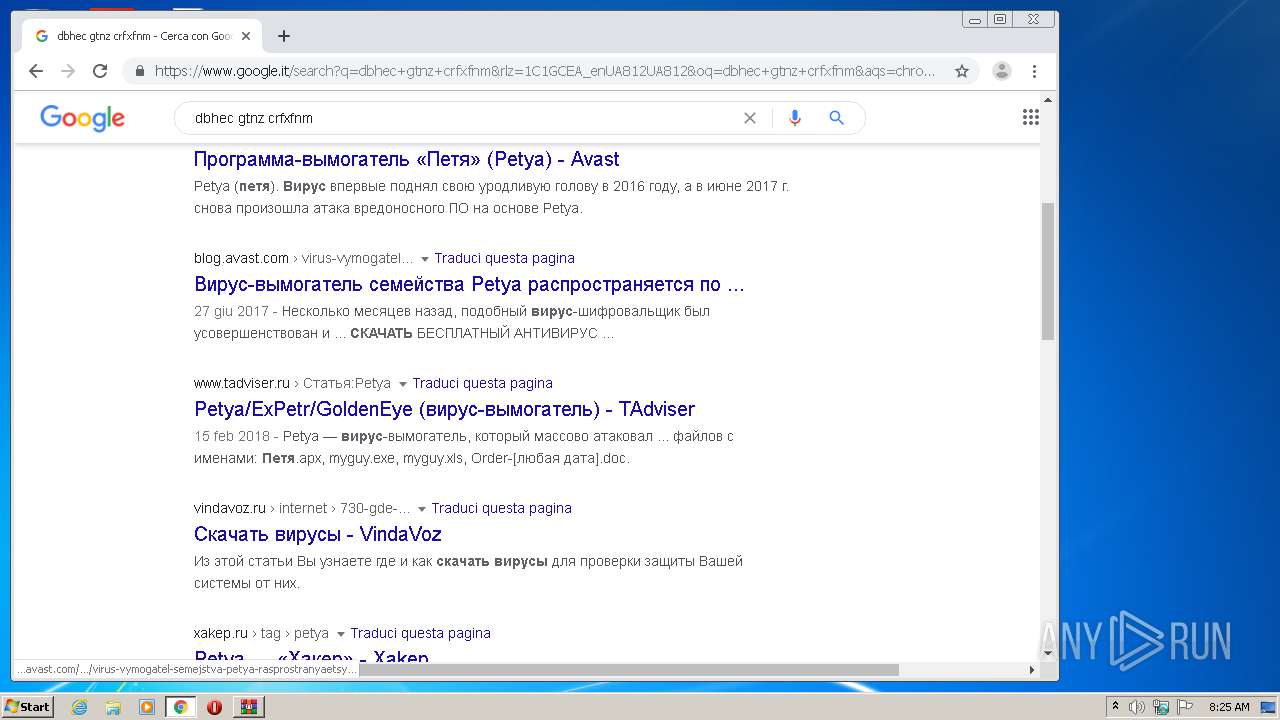
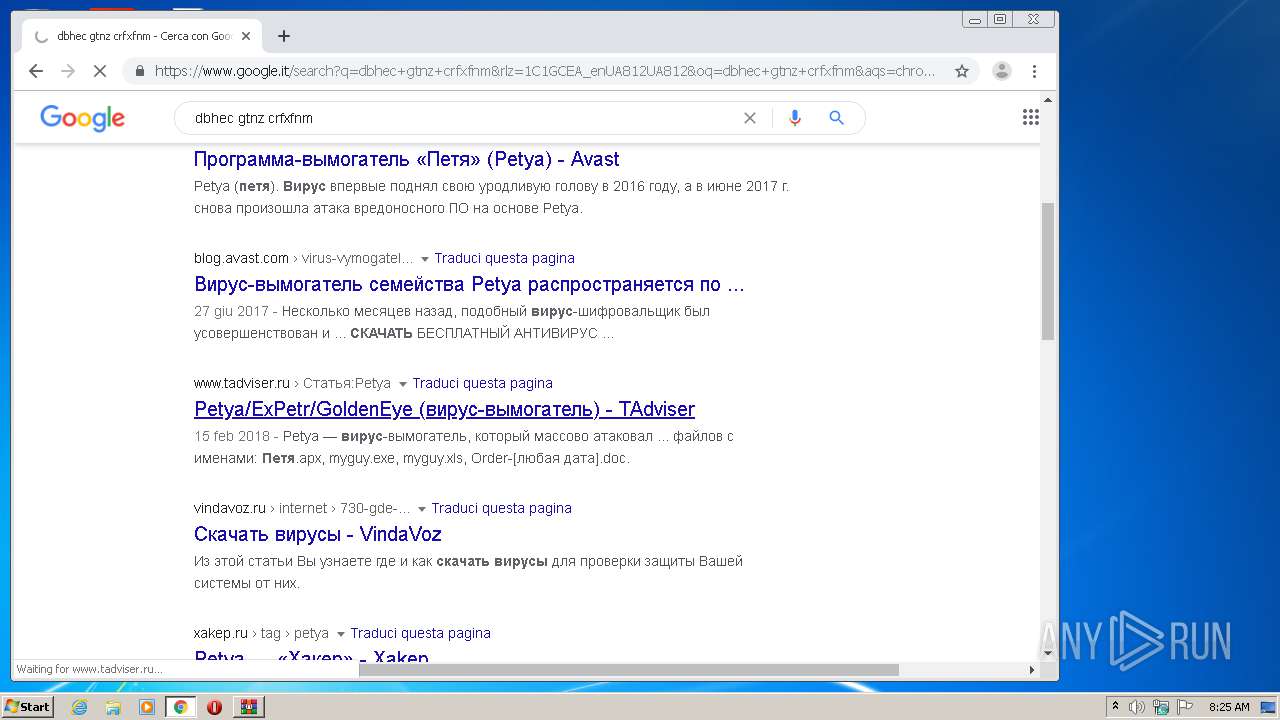
2888 | chrome.exe | GET | — | 185.159.81.170:80 | http://www.tadviser.ru/index.php/%D0%A1%D1%82%D0%B0%D1%82%D1%8C%D1%8F:Petya/ExPetr/GoldenEye_(%D0%B2%D0%B8%D1%80%D1%83%D1%81-%D0%B2%D1%8B%D0%BC%D0%BE%D0%B3%D0%B0%D1%82%D0%B5%D0%BB%D1%8C) | NL | — | — | whitelisted |
2888 | chrome.exe | GET | 204 | 172.217.175.227:80 | http://csi.gstatic.com/csi?v=3&s=gapi_module&action=gapi_iframes__googleapis_cli12&it=mli.5,mei.3&tbsrt=491&tran=15&e=abc_l0,abc_m0,abc_pgapi_iframes__googleapis_cli12,abc_u0&rt= | US | — | — | whitelisted |
2888 | chrome.exe | GET | 200 | 172.217.132.103:80 | http://r2---sn-5hne6nsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.128.27.133&mm=28&mn=sn-5hne6nsy&ms=nvh&mt=1591514596&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2888 | chrome.exe | GET | 200 | 209.85.226.73:80 | http://r4---sn-5hnekn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.128.27.133&mm=28&mn=sn-5hnekn7k&ms=nvh&mt=1591514655&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2888 | chrome.exe | GET | 200 | 91.218.228.14:80 | http://vindavoz.ru/templates/vindanew/style/styles.css | RU | text | 4.49 Kb | whitelisted |
2888 | chrome.exe | GET | 200 | 91.218.228.14:80 | http://vindavoz.ru/templates/vindanew/style/engine.css | RU | text | 6.24 Kb | whitelisted |
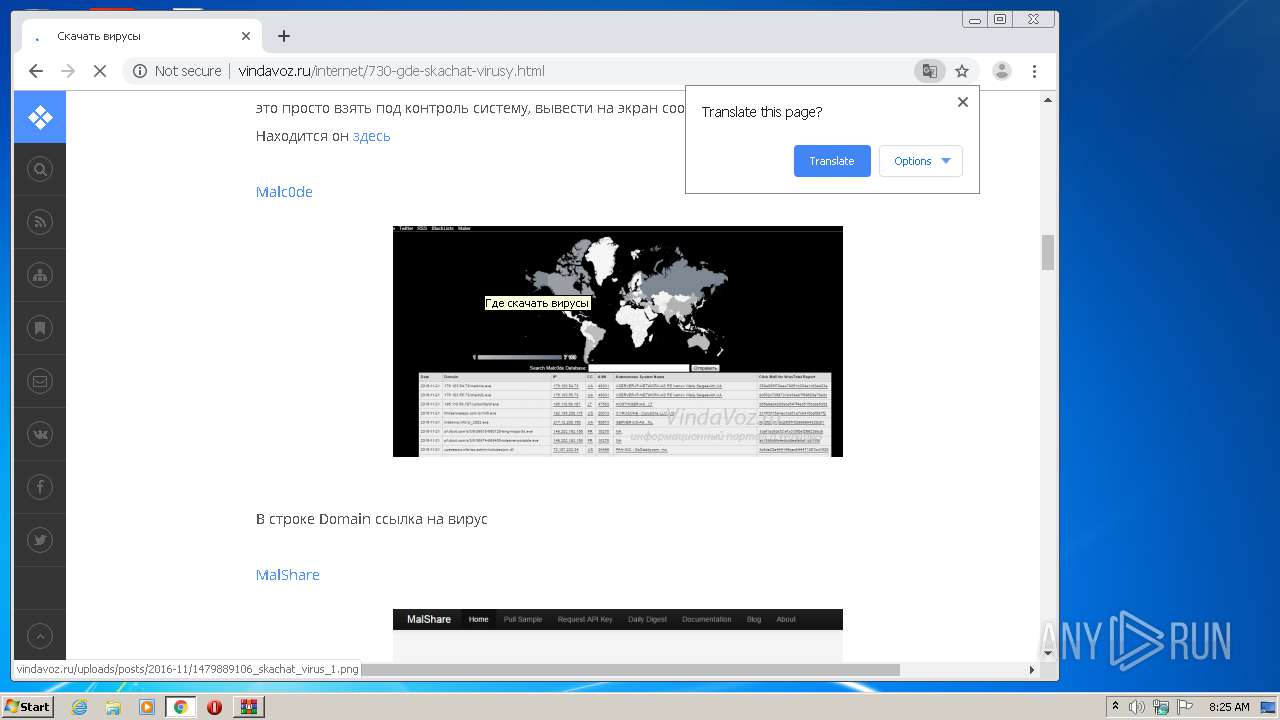
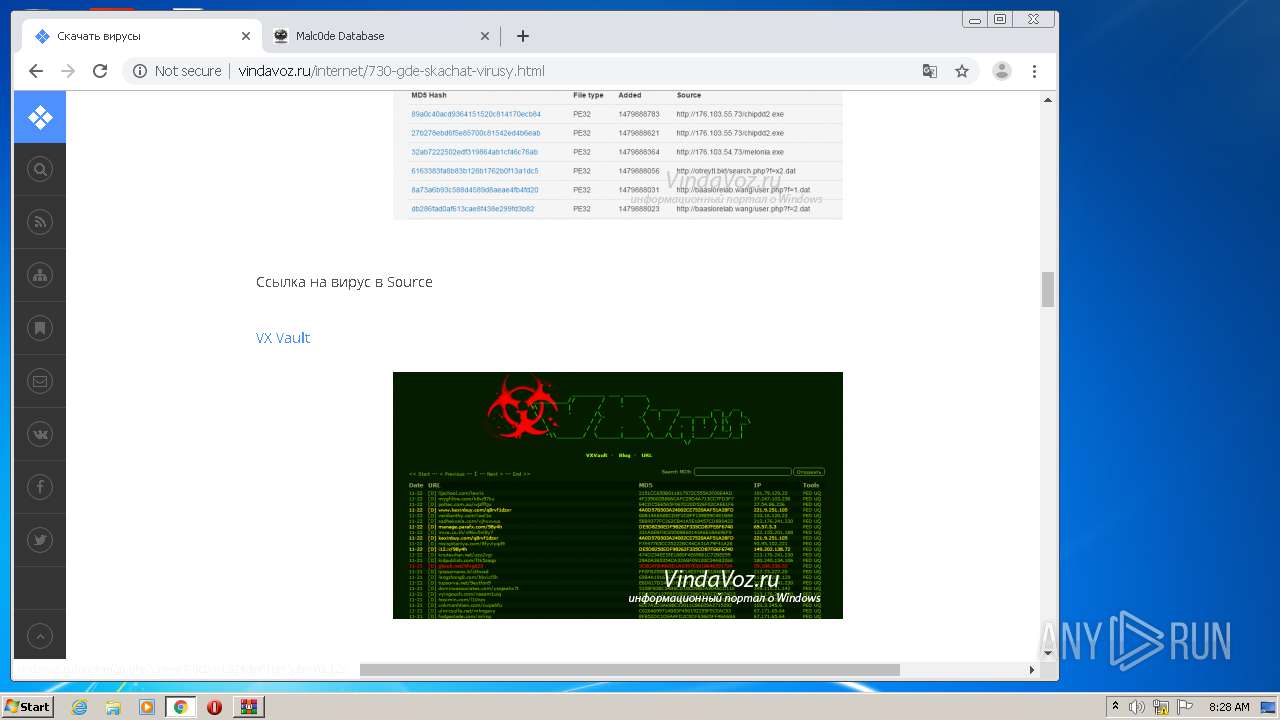
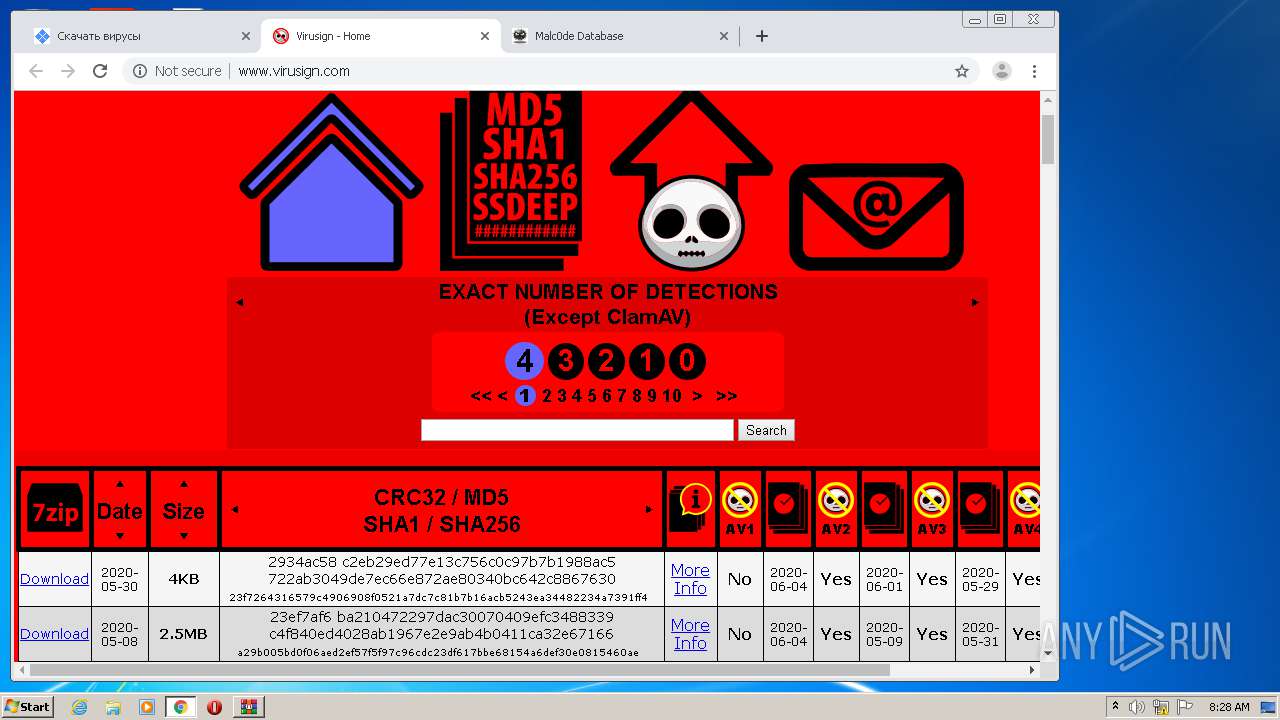
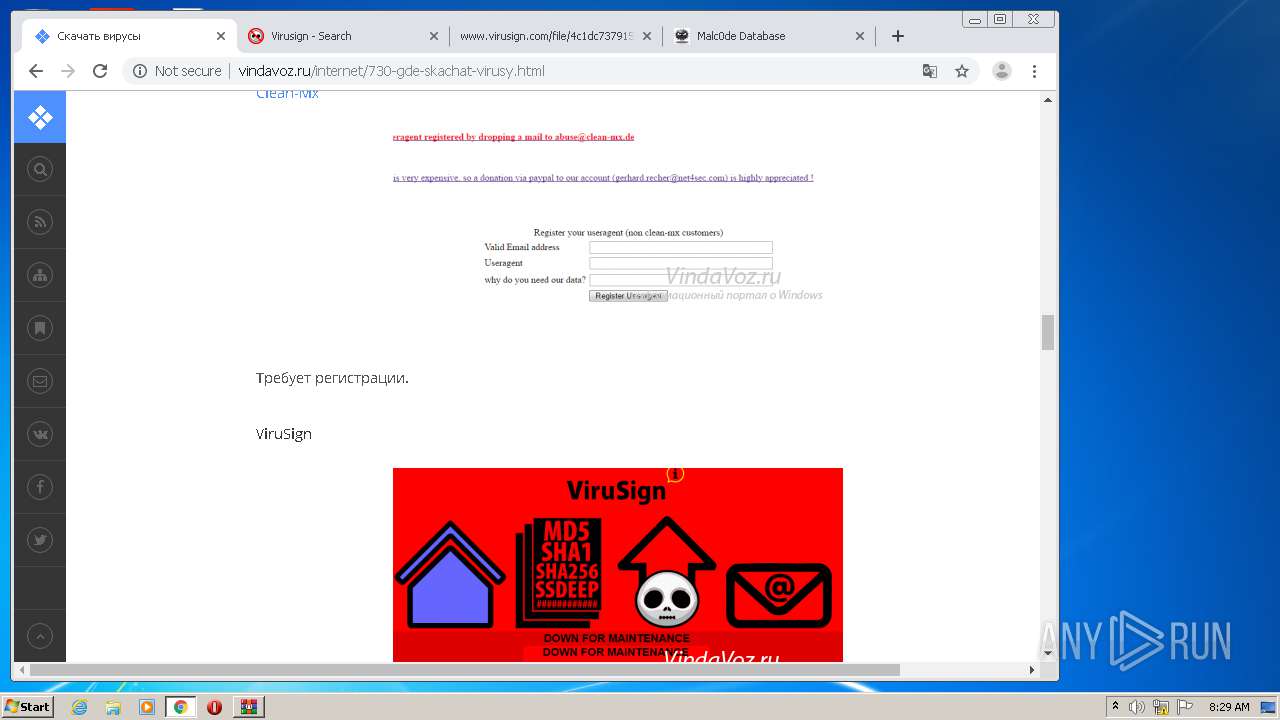
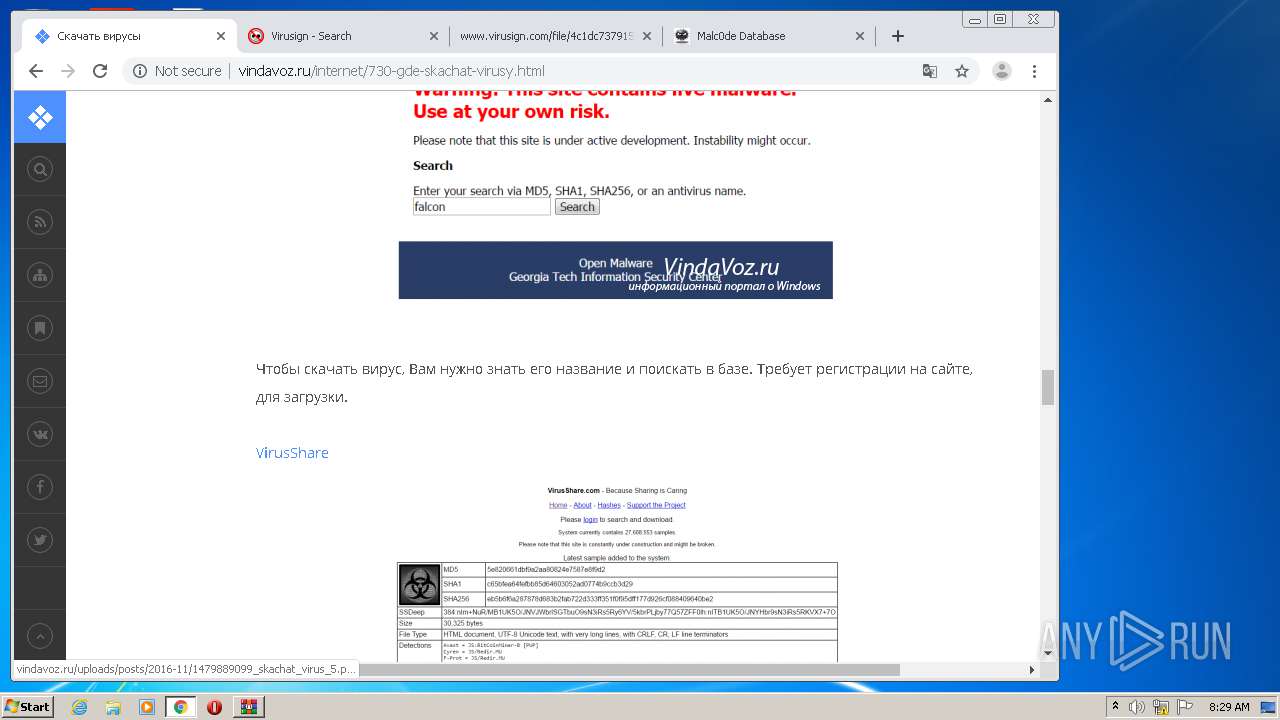
2888 | chrome.exe | GET | 200 | 91.218.228.14:80 | http://vindavoz.ru/internet/730-gde-skachat-virusy.html | RU | html | 16.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2888 | chrome.exe | 172.217.22.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2888 | chrome.exe | 216.58.207.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2888 | chrome.exe | 216.58.208.46:443 | play.google.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 172.217.132.103:80 | r2---sn-5hne6nsy.gvt1.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.227:443 | www.google.it | Google Inc. | US | whitelisted |
2888 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2888 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
play.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2888 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Outgoing Basic Auth Base64 HTTP Password detected unencrypted |